Securely scale your Web Apps with Azure Front Door
There is a big buzz out there about Azure Front Door. Is it a Load Balancer? A CDN? A Traffic Manager? A Web Application Firewall ? A Reverse Proxy? An Application Gateway?
So, what is Azure Front Door?
Azure Front Door actually is all the above and more. It is a global service, that routes web traffic based on performance and availability. A Layer 7 multi-region load balancer with Web Application Firewall (WAF) capabilities, DDoS protection & CDN.
Azure Front Door is the entry point, the edge, of all Microsoft’s WAN. All Microsoft services, like Office 365 & Bing, are using Azure Front Door.
The services that Azure Front door provides are:
- Accelerate application performance
- Increase application availability with smart health probes
- URL-based routing
- Multi-site hosting
- URL redirection
- Session affinity
- SSL termination
- Custom Domain & certificate management
- Security via custom WAF rules
- DDoS protection
- URL rewrite
- IPv6 and HTTP/2 support
At Azure Front Door documentation there is a paragraph that can help to understand the difference between Azure Front Door and other publishing / load balancing Azure solutions and where to use each.
Azure provides a suite of fully managed load-balancing solutions for your scenarios. If you are looking for a DNS based global routing and do not have requirements for Transport Layer Security (TLS) protocol termination (“SSL offload”) or per-HTTP/HTTPS request, application-layer processing, review Traffic Manager. If you are looking for load balancing between your servers in a region, for application layer, review Application Gateway and for network layer load balancing, review Load Balancer. Your end-to-end scenarios might benefit from combining these solutions as needed.
For pricing information, see Front Door Pricing.
How to scale your web apps with Front Door
Create two simple Azure Web apps. Check this guide for a simple guide on how to create Azure App Service: https://www.e-apostolidis.gr/microsoft/azure/azure-start-point-your-first-web-app/
One at West Europe:

and one at North Europe:

Using FTP, I deployed an one-page html site at both regions. I change the text of both site to say “This Web Site is located at North Europe Azure Datacenter”

and “West Europe” to the other.

Then create a Front Door. Search for Front Door at Azure marketplace and Create one.

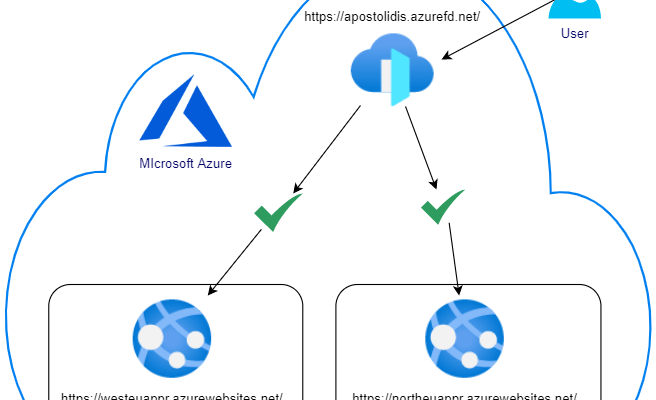
This is a high level diagram of the Front Door with two Web Apps design that we will create

The “create a Front Door” wizard will start and we can configure it step by step. First we will create a Frontend host by clicking the + at the Step 1

At the frontend host we will create the URL that our apps will be available. I added the papostolidis.azurefd.net. of course later you can add your custom domain and add a CNAME to route the traffic to the Front Door.

Then, at the Backend pools (Step 2), press the + to add the web apps. add a name for the backend pool, like “myapps” and press + ADD a backend to add the apps.

Select host type, you can add app service, cloud service, storage and custom host (URL). I selected the app service.

Select the subscription and the app service and add the correct ports for http and https traffic.
The priority defines if the traffic will be routed to the host with the lower priority number (e.g. 1) and if that host fails will route to the next host with bigger priority number (e.g. 2). If you add the same priority to more than one host then it will follow the weight number.
The weight number defines the percentage of requests that will be routed to each host.

The same way add the second web app

Finally select a path, protocol and interval for the probe that will do health checks to the app to define if it is active or not.

The third step is to add the routing rules. At the routing rules you can specify:
- The accepted protocol, http or https.
- the frontend host for this rule
- the patterns that the route will accept, like www.e-apostolidis.gr/mysite/* or just /* ro root.
- Route type forward or redirect.
- The backend pool that this rule will direct the traffic
- The protocol that the traffic will be forwarded. Here we define the SSL Offload if we select HTTPs for frontend accepted protocol and HTTP for backend.
- URL Rewrite rules
- Caching, for static content caching like CDN.

Once all steps are completed we can move on and create the Front Door

When the Front Door is ready, we can see the URL at the Overview.

And browse our web app using the Front Door URL:

How to protect your web apps with Front Door
Right now we scaled our web apps. If we use each app’s URL we can still access the app. The first security step is to lock the web apps to be accessed only through the Front Door URL.
Checking the Azure Front Door FAQ page, https://docs.microsoft.com/en-us/azure/frontdoor/front-door-faq it lists the Front Door’s address rance.
Front Door’s IPv4 backend IP space: 147.243.0.0/16
Go to the App Service, at the Networking section, select “Configure Access Restrictions”

Add an allow access restriction with the IP range of the Front Door.

Automatically a Deny rule will be created for everything else.

Add the rule to both web apps and then try to access the apps with their direct links.

Now on, we can access the apps only by using the Front Door URL:

This is a high level diagram after the restrictions

At the next article, we will see how to add Web Application Firewall (WAF) Rules to Front Door, Stay Tuned!!

Pantelis Apostolidis is a Sr. Specialist, Azure at Microsoft and a former Microsoft Azure MVP. For the last 20 years, Pantelis has been involved to major cloud projects in Greece and abroad, helping companies to adopt and deploy cloud technologies, driving business value. He is entitled to a lot of Microsoft Expert Certifications, demonstrating his proven experience in delivering high quality solutions. He is an author, blogger and he is acting as a spokesperson for conferences, workshops and webinars. He is also an active member of several communities as a moderator in azureheads.gr and autoexec.gr. Follow him on Twitter @papostolidis.

Hi,
for drupal 8 on webapp with front door on azure
edit settings.php with
$settings[‘reverse_proxy’] = TRUE;
$settings[‘reverse_proxy_addresses’] = array($_SERVER[‘REMOTE_ADDR’]);
best regards
Juan Rendon
Thank you for the update Juan !
Hi,
In my ‘Custom forwarding path’ contain query string ‘/mydevice/mylogin?myaccount=d2’ and the AFD routing rule return error “Pattern must start with a / and contain only valid characters according to RFC3986 Section 3.3 and must not contain query string parameters..”
How do I handle the query string ‘?…’ in the custom path?
Thanks.